The BiDigest architecture
Closing the consequence gap in <50ms.
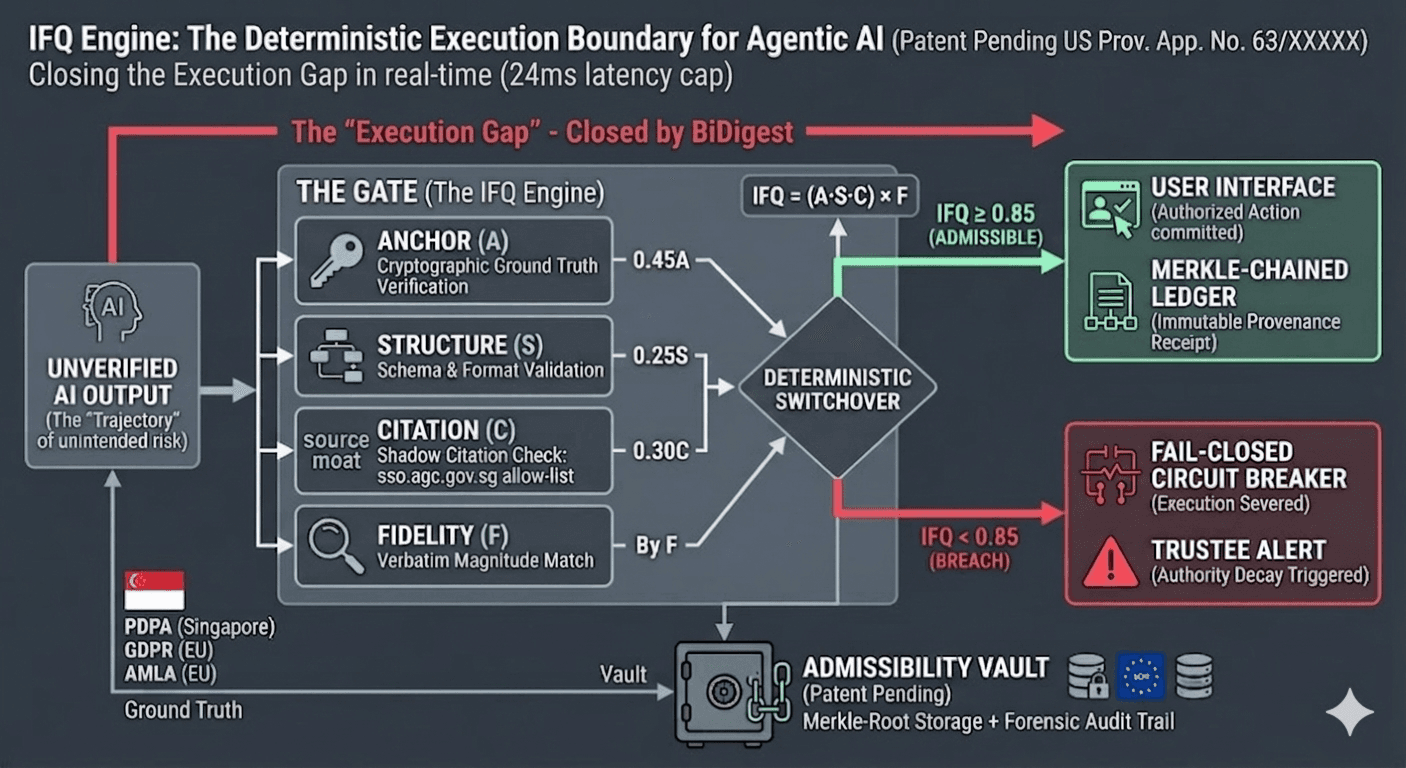
Why "monitoring" isn't enough: dashboards detect drift after execution. BiDigest is an enforcement layer — a synchronous intercept at the commit boundary so inadmissible payloads fail closed before they become operational fact.
We don't ask your AI to be safe. We make it impossible for it to be inadmissible at the boundary — or it does not execute.
Not a wrapper — a synchronous intercept
Wrappers and prompt filters operate around the model. BiDigest evaluates the proposed execution against Ground Truth, schema contracts, and Triple-Lock consensus on a deterministic path. Integrators wire the admissibility API or use the SDK-shaped client so the same physics applies in CI and production.
The SDK and the physics
The @bidigest/sdk package exposes a small, strict client for calling /api/v1/admissibility/verify with typed contracts — so "admissibility" is an API outcome, not a slide deck. Pair it with the mechanical constraints on the features page (Triple-Lock, forensic ledger, jurisdiction-aware SKB).
The execution graph
Dual-boundary governance in one linear path—from Ground Truth upstream to the commit boundary downstream.
Control plane & IFQ at the boundary (US Prov. App. No. 63/XXXXX)
Phase 1: Ground Truth anchoring
You define the admissible state space. We ingest your regulatory identifiers, statutory anchors, and hard corporate policies—encrypting them into an immutable Ground Truth baseline.Phase 2: Synchronous intent interception
When your AI model (or a third-party vendor’s AI) emits a response or proposes a state-change, the BiDigest Control Plane performs a synchronous intercept on the wire: the payload is evaluated before it reaches client surfaces or systems of record. This is not post-generation filtering and not a prompt-only wrapper.Phase 3: The IFQ calculation & Triple-Lock
In under 50 milliseconds, our patent-pending IFQ Engine scores the payload's intent against your Ground Truth. The system demands a deterministic Triple-Lock (cryptographic sign-off from Legal, Risk, and Engineering).Phase 4: Fail-closed or admitted execution
If the IFQ score drops below the defined threshold, the Commit Boundary mathematically fails closed (the action is blocked). If authorized, the action executes and generates a Merkle-chained Admissibility Receipt.
Sandbox walkthrough — packet to Commit Boundary
On the homepage, the Commit Boundary showcase uses the toggles to switch authorized vs fail-closed stories. When public/videos/admissibility.mp4 and fail-closed.mp4 are present, it plays those loops; otherwise it uses an in-browser motion fallback (no missing-file 404s). See public/videos/README.md in the repo.
- Home — Commit Boundary showcase
- State of Admissibility 2026 — embedded commit-boundary narrative videos (governance reader).
- Test the Physics — run synthetic payloads in the public sandbox.
The IFQ engine (patent pending)
We do not rely on probabilistic LLM "safety" prompts. Admissibility is a mathematical certainty. The Identity Fidelity Quotient (IFQ) is calculated at the execution boundary:
Patent pending — US Prov. App. No. 63/XXXXX
The three pillars of IFQ
Identity (A — Anchor)
Matches the payload against hard tokens from your Ground Truth. We rely on statutory anchors, not paraphrased blog summaries, to drive what the gate may admit.
Structure (S — Schema)
Ensures requests and payloads satisfy structural contracts at the boundary. “Valid JSON” cannot be used to mask invalid regulatory obligations.
Citation & fidelity (C × F)
Enforces citation integrity. Shadow Sources (outdated or rogue URLs) must be on your allow-list. Fidelity (F) acts as the multiplier, mathematically tying the output tokens back to the anchored reference text. A “right answer” from the “wrong source” yields an IFQ of zero.
Merkle-chained forensics
In regulated industries, an action didn't happen unless you can prove why it happened. Every admitted execution generates a cryptographic Admissibility Receipt.
- Tamper-proof ledger: a SHA-256 hashed record of the exact AI payload, the IFQ calculation, and the Ground Truth anchor used at the moment of execution.
- Audit ready: export the enforcement path for your insurers, the SEC, or Bank of England PRA supervisors.
Intercept in action — fail-closed report
The last step from trial to purchase is seeing a real intercept: an inadmissible intent blocked before it mutates a system of record, with a receipt-shaped artifact your CCO can file. We will publish a sanitized fail-closed case study here as soon as it clears review — in the meantime, run the public sandbox and home showcase to watch the same boundary behavior on synthetic payloads.
- Test the Physics — synthetic payloads against the Triple-Lock demo.
- Home — Commit Boundary showcase (authorized vs fail-closed video loops).
Deploy the control plane
Trustee tier
The standard for regulated SMEs
- • Access to the IFQ Engine and the <50ms Commit Boundary.
- • Weekly drift analytics and Shadow Source detection.
Sovereign tier
Advanced executions & citations
- • Full Merkle-chained admissibility receipts for every transaction.
- • Strict Citation Integrity (C) enforcement to block unauthorized data ingestion.
- • Continuous compliance mapping for the EU AI Act and NIST 800-171.
Full technical spec on the Sovereign Tier page; PDF exports where offered in-product.
Trustee handbook (Markdown): Open Trustee Tier handbook